By 2024, the IoT world has seen substantial growth, with a multitude of devices seamlessly integrating into our everyday lives. Take the healthcare sector, for instance, where IoT devices have become indispensable. IV pumps, patient monitors, and glucometers are just a few examples that underscore the deep integration of IoT in daily healthcare routines, demonstrating its pivotal role in patient care.
The Industrial Internet of Things (IIoT) harnesses the power of IoT to create intelligent machines capable of autonomous communication and decision-making. This evolution towards smart factories forms a vital component of the larger paradigm shift known as Industry 4.0. Technologies such as IoT, AI, and big data are driving forces behind this manufacturing revolution. Consider Germany, where a striking 84% of manufacturers aim to invest a substantial €10 billion (approximately $10.52 billion) annually in IoT solutions by 2025. This broad adoption underscores the transformative and significant impact of IoT in industrial settings.
The Arrival of 5G
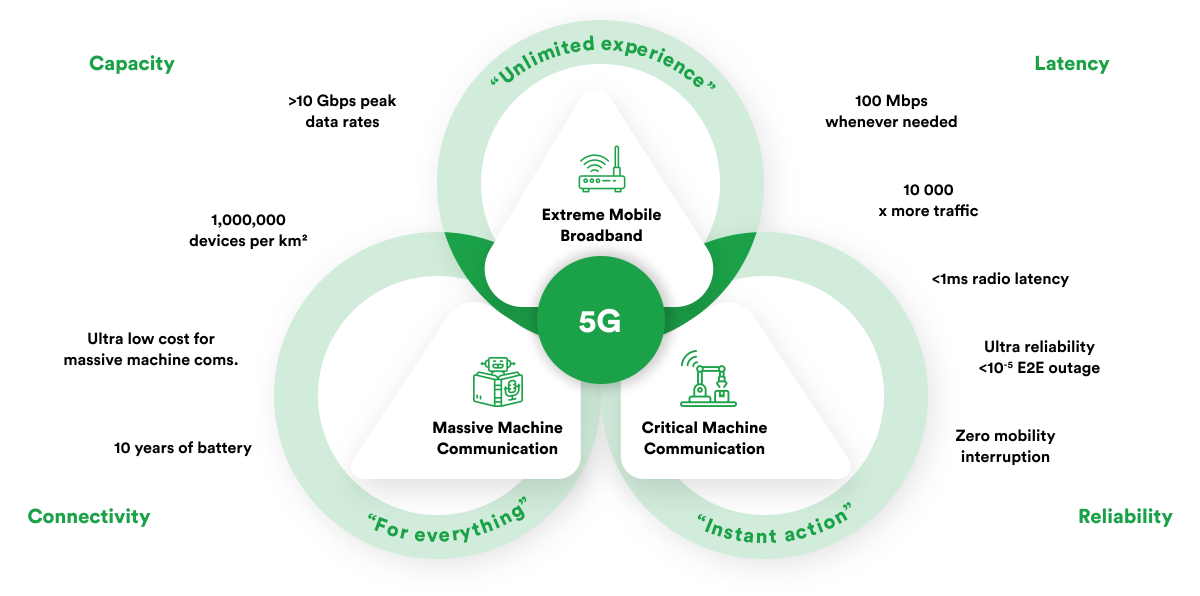
5G technology represents the newest cellular technology advancement, designed to boost wireless networks’ speed and responsiveness significantly. With 5G, wireless broadband connections could achieve speeds up to 20 Gbps, according to some estimates, faster than wired networks and offer ultra-low latency of 1 millisecond or less for real-time applications. Thanks to its broader bandwidth and complex antenna technology, 5G is tailored to accommodate a substantial increase in data transmission over wireless systems.
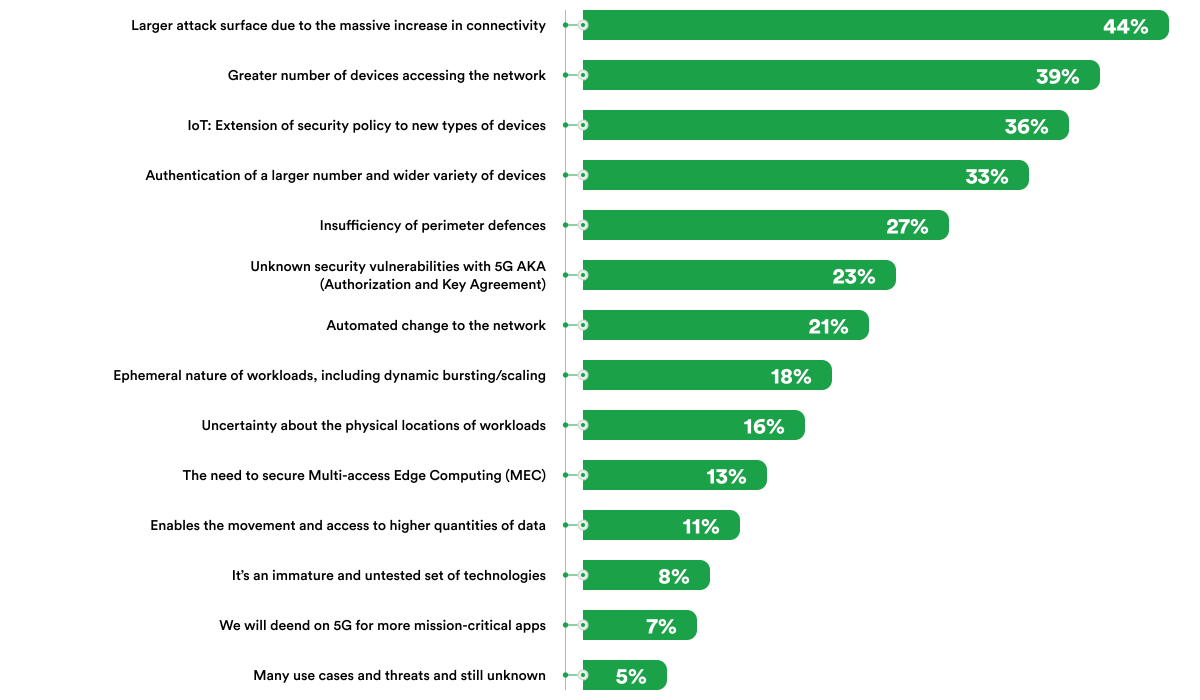
The nature of 5G networks also poses specific challenges. The arrival of 5G technology marks a significant shift in digital connectivity, bringing advancements far surpassing its predecessors and set to revolutionize our interaction with the internet. One of its standout features is supporting over a million devices per square kilometer, a crucial factor for the promising Internet of Things networks. Additionally, 5G features peak data rates that exceed 10 Gbps, enabling incredibly high-speed mobile broadband.
A key attribute of 5G is its ultra-low latency, less than one millisecond, which opens doors for real-time, critical machine-type communications. Furthermore, its ultra-reliability, with almost zero end-to-end outages, guarantees consistent connectivity, which is essential for mission-critical applications. These combined features lay the foundation for a new digital transformation era, positioning 5G as a central player in the evolution of interconnected devices and services.
Merging IoT and 5G Technology
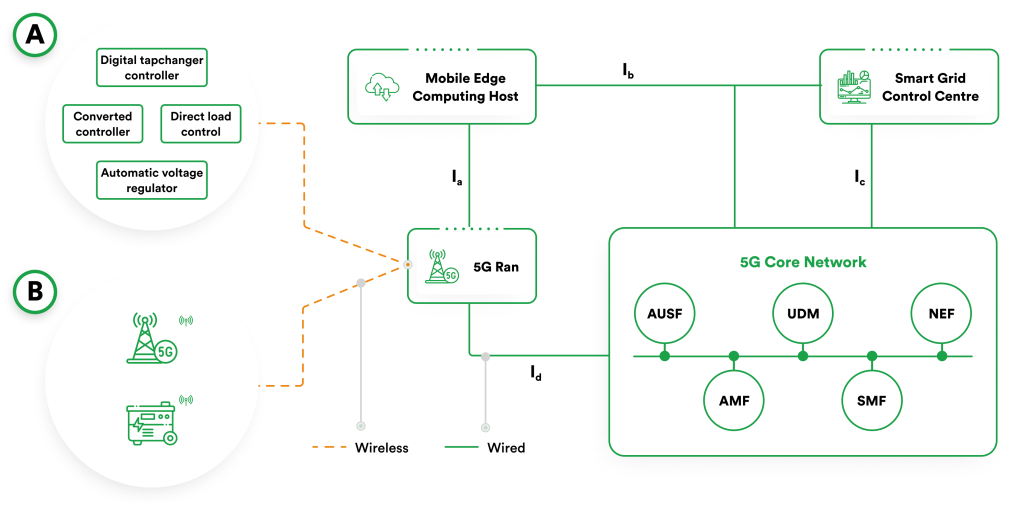
The merger of IoT and 5G technology is a key element in the evolution of modern tech. The high-speed, low-latency nature of 5G is ideally suited to meet the demands of an extensive IoT network. It provides the required bandwidth and speed to manage the data from billions of IoT devices. This synergy is opening exciting new possibilities across various sectors. In smart cities, for instance, 5G can significantly boost IoT applications in areas such as traffic management, public safety, and environmental monitoring, offering real-time data analysis and enhancing city services.
In healthcare, IoT and 5G drives progress in telemedicine and patient monitoring. It enables the real-time transmission of data, which can be crucial in saving lives. The increasing number of IoT devices in healthcare, which is expected to generate up to $108.60 billion in revenue by 2024, underscores the vast potential of this integration. In agriculture, IoT devices used for monitoring crop health, soil conditions, and weather can be significantly improved with the capabilities of 5G, leading to more efficient and productive farming practices.