6. Integration of AI and Machine Learning in Security
This trend reflects a significant evolution in how security threats are predicted, detected, and resolved, leveraging the capabilities of AI and ML to analyze vast datasets, recognize patterns, and automate decision-making processes. The application of these advanced technologies in security not only enhances the ability to identify and respond to threats in real time but also significantly improves the efficiency and effectiveness of security operations within the fast-paced, complex environments of modern software development. AI and machine learning capabilities have matured significantly, with more organizations deploying these technologies for predictive threat detection and automated security response.
AI and ML algorithms are being deployed across various security fields within DevSecOps, from automated threat detection to behavior analysis and anomaly detection. These technologies excel in environments where the volume and velocity of data exceed human capacity for analysis, enabling proactive security measures that can adapt to the evolving threat landscape. For instance, ML models can be trained on historical security incident data to predict potential vulnerabilities and threats, allowing organizations to strengthen their defenses before breaches occur. Similarly, AI-driven security tools can monitor network traffic and user behavior in real-time, identifying unusual patterns that may indicate a security threat and enabling swift, automated responses to resolve potential damage.
7. Compliance as Code
This innovative approach leverages the power of automation and version control to ensure that compliance is systematically integrated into every stage of the software lifecycle, from initial design to deployment and maintenance. As organizations navigate an increasingly complex regulatory environment, with strict requirements across different jurisdictions and industries, Compliance as Code emerges as a strategic tactic to streamline compliance processes, reduce the risk of non-compliance, and enhance overall operational efficiency.
Compliance as Code transforms traditional compliance activities, which are often manual, time-consuming, and prone to human error, into automated, repeatable, and reliable processes. By defining compliance requirements as code, organizations can leverage automated tools to continuously monitor and enforce compliance across their IT infrastructure and applications.
The rise of Compliance as Code is closely aligned with the broader adoption of Infrastructure as Code (IaC) and Policy as Code practices within DevSecOps. Together, these practices create a cohesive framework for managing security, compliance, and infrastructure through code, enabling organizations to deploy applications rapidly and securely while adhering to regulatory standards. For example, organizations can use IaC tools to automatically apply security configurations that comply with industry standards, such as the CIS Benchmarks, and use Compliance as Code to continuously validate these configurations against the standards.
8. Increased Use of Open-Source Security Tools
The eighth significant trend in the evolution of DevSecOps in 2024 is the increased use of open-source security tools. This trend signifies a shift towards leveraging open source projects’ collaborative, transparent nature to strengthen the security of software development and deployment processes. Open-source security tools, developed and maintained by a global community of security professionals and enthusiasts, offer a range of advantages, including cost efficiency, flexibility, and the rapid adoption of community-driven insights and advancements in threat detection and mitigation. This democratization of security tools has enabled organizations of all sizes to access complex security capabilities, previously the domain of only well-resourced companies.
The increase in open-source security tools is driven by the growing complexity of cyber threats and the need for agile, adaptable security solutions that can be integrated seamlessly into the DevSecOps workflow. Tools such as vulnerability scanners, static and dynamic code analyzers, and infrastructure as code (IaC) security checkers are now staples in the DevSecOps toolchain, providing critical capabilities for identifying and addressing vulnerabilities at every stage of the software development lifecycle. These tools are designed to fit into the continuous integration and continuous deployment (CI/CD) pipelines, enabling automated security checks that do not inhibit development speed.
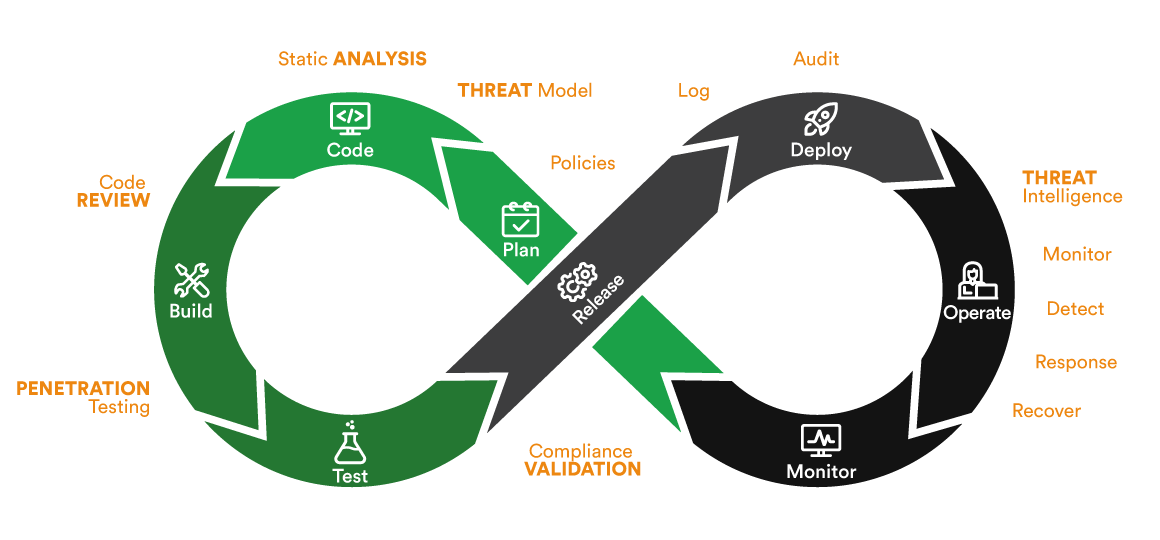
9. Growing Importance of Threat Modeling
This strategic practice, vital for identifying, assessing, and addressing potential security threats early in the software development lifecycle, has become increasingly critical as applications grow in complexity and the cyber threat landscape continues to evolve. Threat modeling enables organizations to systematically analyze their applications, systems, and business processes to identify vulnerabilities that attackers could exploit, prioritize them based on their potential impact, and develop mitigation strategies to address them. This proactive approach to security perfectly aligns with the DevSecOps methods of integrating security considerations from the outset of the development process.
The significance of threat modeling in 2024 stems from its ability to provide a structured framework for understanding the security implications of design decisions and architectural choices. By simulating potential attack scenarios and identifying exploitable weaknesses before they are coded into the application, developers and security teams can work together to design more secure systems from the ground up. This collaboration is facilitated by various methodologies and tools designed to support threat modeling, such as STRIDE (Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, Elevation of Privilege) and DREAD (Damage, Reproducibility, Exploitability, Affected Users, Discoverability), which help teams systematically evaluate and address security risks.
Emphasis on Privacy by Design
Privacy by Design, increasingly pivotal in the digital age, advocates for integrating privacy and data protection considerations from the earliest stages of the design and development process. As global awareness and regulatory demands around data privacy intensify, Privacy by Design has transitioned from a forward-thinking approach to an essential element of software development and operational practices. This trend underscores the growing recognition that privacy cannot be an afterthought, or a feature added post-development but must be an intrinsic part of the product lifecycle, from conception to deployment.
The emphasis on Privacy by Design in 2025 is primarily driven by the expanding landscape of data protection regulations, such as the General Data Protection Regulation (GDPR) in the European Union, the California Consumer Privacy Act (CCPA), and other similar laws worldwide. These regulations require strict data handling and privacy protections, compelling organizations to adopt privacy-centric practices or face significant penalties. Privacy by Design addresses these requirements by ensuring that privacy controls are embedded into the technology, enabling organizations to meet compliance regulations more naturally and effectively.